Anatomy of a Phishing Attack
A well-known Connecticut business recently hired Kelser to hack them with a simulated phishing attack. Here’s how we did it.
Over the past year, we’ve been working with Hoffman Auto Group, one of Connecticut’s largest auto dealers, to strengthen their cybersecurity posture and make sure their customer data is as safe as possible. After putting all the latest technology in place, it came time to address employee awareness since most cyber-attacks involve human error.
In order to establish a baseline, we decided to launch a simulated phishing attack. New Haven, Connecticut, ABC affiliate WTNH documented the process in a recent story. This post explores in more detail how we created the phishing attack. It’s a behind-the-scenes look at techniques hackers use and how to spot them.
Go Phish
Everyone remembers their first email from a foreign prince. He just needs to get his fortune out of his country. Can he please wire the money to your bank account? He just needs the account numbers.
This was the earliest form of phishing—using phony emails to glean usernames, passwords, credit card numbers, and more. While everyone is hip to this scam, phishing is still the preferred method of hackers and the way most cyber-attacks start. However, the techniques have come a long way.
Rather than just asking for personal information, phishing attacks these days try to trick the recipient into clicking on a link, or “phish hook,” that appears to come from a reliable source. A successful phishing attack can put a company’s confidential information at great risk.
Often, the phishing email includes personal information that makes it seem real. This information is collected from online sources such as LinkedIn or the company website and used to deceive the recipient in what is called “spear phishing.”
Though the techniques have become more sophisticated, phishing attacks are relatively easy to do. Here’s how our team at Kelser created an email for Hoffman Auto Group designed to trick employees into clicking on a phish hook.
How We Created Our Phishing Email
Step 1: Reconnaissance
To simulate the process of a real hacker, we assigned this project to Kelser team members who had no previous contact with Hoffman. We didn’t share any of our information about the company with them either. Using a VPN (virtual private network) to avoid detection, they combed the internet for publicly available information about Hoffman that could be used to trick employees. They paid particular attention to the corporate structure, because a phishing email from a trusted company leader usually works best.
Using LinkedIn filters, it was easy to find everyone with a Hoffman Auto Group email account. Christine Pakutka, Hoffman’s IT Director, seemed an ideal choice for the person to “spoof,” or to fake as the sender of the email. The assumption was that employees receiving an email from Christine asking them to click a link or change their password would be believable.
Step 2: The Devil’s in the Details
The next step was to learn the email structure Hoffman uses. By searching “intext: hoffmanauto.com” in Google, our ethical hackers determined that their email addresses are formatted like this:
firstname.lastname@hoffmanauto.com
The email address that the message should appear to come from was settled, but what should the email say? A small logo at the bottom of Hoffman’s website indicates that the site is managed by dealer.com. Further research revealed that dealer.com is owned by Dealertrack. It seemed safe to assume, then, that Hoffman uses Dealertrack management software. Using a few of the publicly obtained company email addresses to try to do a password reset on the Dealertrack website confirmed this.
The owners of those email accounts at Hoffman might receive a warning from Dealertrack that an attempt was made to change their password, but they would likely ignore it. At this point, our experts had the name of Hoffman’s IT Director, her email address, and the dealer management software the company uses—all relatively easy-to-find information for most companies.
Step 3: Build it Believable
Of course, it’s not enough to have all the information correct--the email has to look real, too. Our team needed to see what the company email signature looks like. All this takes is having an email interaction with someone at the company. Hackers sometimes send fake resumes to HR. In this case, our team enquired about a car listed on one of Hoffman’s websites, received a reply, and with it, a template for the email signature.
Step 4: Drown Skepticism in Urgency
One key ingredient any effective phishing attack will include is a sense of urgency. When something has to be done immediately, it short circuits skepticism. Ironically, we sent a phishing email telling employees of a security breach that required them to reset their Dealertrack passwords. The urgency of the “potential security breach” seemed the easiest way to get them to click on our phish hook.
Finally, our ethical hackers used a private SMTP email server to “spoof” Christine’s email address, and they added her signature so it would appear the message came from her. The email was then sent to every employee whose name was discoverable online. Here’s what the email looked like:

When Hoffman employees clicked on the link, they were presented with a blank blue screen, and we received a notification that they had taken the bait. Had this not been a simulation, we (the hackers) would have obtained the login information for Dealertrack, which could open doors to sensitive data.
Teach a Man to Phish
Unlike many phishing emails, which come from knockoff domains such as hofmanauto.com or hoffrnanauto.com, this email was technically indistinguishable from a real email from Christine. Even though this was a sophisticated attack, a couple of red flags could still have been spotted.
First, the recipients should have been suspicious of the urgent (and unusual) nature of a request to reset their password. Many savvy Hoffman employees recognized this and called Christine or walked into her office to double check.
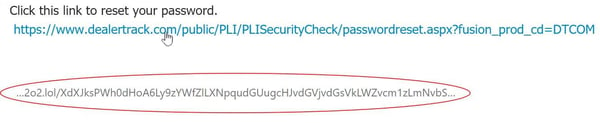
Secondly, though the link appeared legitimate, the simple step of hovering a mouse over it would have revealed a very long string of random letters and numbers—a huge red flag.
This simulated phishing attack was a wakeup call to Hoffman’s employees. Even with the best available technology in place, they learned that the burden of protecting the company’s data rests largely with them. Following this experiment, new procedures were put in place at Hoffman.
Training and awareness are the front-line defenses against phishing attacks. Hackers are getting more and more sophisticated every day, and it’s important for businesses to keep up-to-date with the latest cybersecurity information. At Kelser, our approach with our clients is short, regularly scheduled training sessions or online modules (as short as 5 minutes). This helps keep security on their minds.
How Can Your Company Prevent Phishing Attacks?
While there is no foolproof way to stop phishing attacks, there is much that can be done to prevent them from being successful. Here are a few practical tips to keep in mind when viewing emails:
- Know your sender. Check the name and email address carefully. Are there any transposed letters or numbers? Any strange domain names?
- Look before you click. Hover your cursor over any links to make sure they go where you think they’re going.
- Never click on any link or attachment from an unknown sender.
- Check for incorrect grammar and spelling. Is it poorly written and/or translated?
- Be cautious of any email that asks you to do something urgently.
- Be especially wary of any requests for money or personal/confidential information.
- Finally, if you see or feel anything unusual or suspicious about an email, take the time to contact the sender for verification.
Even though phishing and other forms of hacking are on the rise, they can be defeated with the right tools, training, and awareness.
For more information on this important topic, check out our free eBook right here called “10 Simple Things to Improve Your Company’s Cybersecurity Posture.”




