How to Keep Your Data Safe With Secure IT Asset Disposition
As technology relentlessly pushes forward, you and your organization will undoubtedly need to upgrade your hardware.
However, you can’t simply forget about your old hardware while reaping the benefits of replacing it with the latest and greatest. You should be excited about the upgrade, but how will you transfer data from your old equipment to the new? How will you erase data from the original hardware?
Think you know Secure IT Asset Disposition? Put your knowledge to the test with our quiz:
These are just a few of the questions you’ll want to think about.
In this post, we’ll walk you through the best practices for secure IT asset disposition (ITAD), and measures you can to take to ensure these practices are being followed.
The 2 Biggest Reasons Secure IT Asset Disposition is Essential
When it comes to your IT, data security and compliance can't be understated. They’re simply two of the more vital IT responsibilities. ITAD is yet another category in which these two responsibilities are key.
Data Security
In 2013, someone was able to purchase an old computer at an auction. The computer happened to belong to the National Health Service in the UK. It also happened to house over 3,000 patient records on its hard drive.
The NHS switched IT asset disposition partners, but failed to follow up after the swap. Their arrangement was typical – the company could sell the old equipment after the hard drives were wiped. The ITAD company believed that physically destroying the hard drives also destroyed the data. They didn’t actually wipe the drives.
After reclaiming another 39 computers, the company found three hard drives with more patient data. Thankfully, the person who purchased the health service’s computers was not a malicious hacker. He was not trying to access strangers’ social security numbers and personal information. He was simply buying a used computer online. He just so happened to discover the data on his “new” computer’s hard drive.
If those computers or drives had gotten into the wrong hands, those patients would have been victims of identity theft or financial fraud.
Hard drives are not the only source you have to worry about. Embedded data is a growing source of concern. For example, innovations like the Internet of Things, or IoT allows us to be connected 24/7 to the internet and each other. While this interconnectedness allows us to be more efficient and productive, it also means that data from all of these devices is constantly collected, stored, and monitored. This is where the danger lies.
There is a general lack of awareness and understanding about what comprises embedded data, where it resides, and the threat it poses. Embedded data is in servers, laptops, tablets, smartphones, medical devices, HVAC systems, smart PDUs, and many others. All of these devices could present immediate risks to your business. Their data often can include network credentials or login information that a cybercriminal can use to access your systems. Without proper asset disposal, you may put your company and customers at risk.
Federal Regulation and Compliance
Due to rampant cyber crime, regulators have given businesses additional reasons to better protect their data. The NHS, for example, was fined £200,000 (equivalent to $300,000) due to their inability to dispose of their assets in a secure manner.
Companies subject to regulations like HIPAA must worry about compliance in addition to their normal IT security practices. HIPAA requires that organizations adopt proper administrative, technical and physical safeguards that makes sure their patient data is protected. It should come as no surprise that the secure disposal of IT assets is covered under the rules.
Federal agencies subject to FISMA are required to create, document and implement data security programs. FISMA also requires the National Institute of Standards and Technology (NIST) to develop standards and guidelines to help federal organizations improve the security of federal information and information systems. Of course, there are several other regulations you may have to comply with depending on your business.
If the equipment you dispose of, resell or donate is poorly managed, your business could be subject to a security breach.
How to Securely Dispose of Your IT Assets
Most organizations rely on the expertise of third parties to securely transfer their data, completely wipe it from old machines and dispose of assets. Those parties typically follow a process like the following:
- Protection and encryption – As early as possible in the process, you’ll want to take the precautionary measure of encrypting your data. It’s always better to be proactive than reactive.
- Deleting and wiping – Next, you’ll want to securely clean your hardware of the data on its drives and other components.
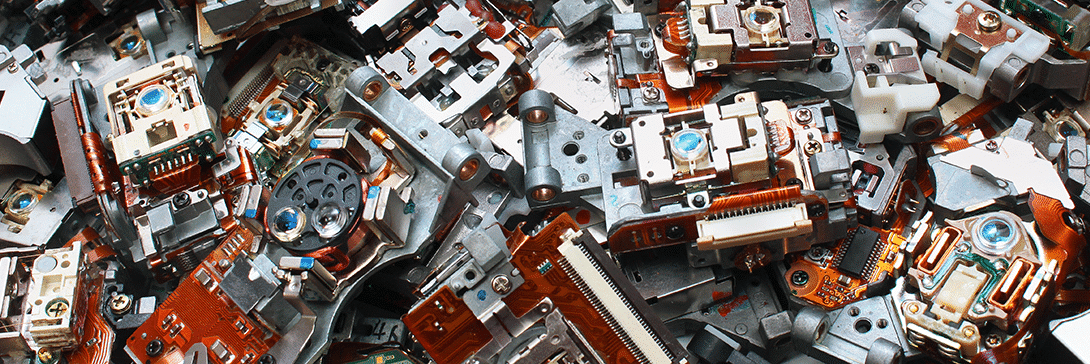
- Destroying – If you have no plans of selling or donating your hardware, you’ll want to safely destroy it.
Using a Third Party For IT Asset Disposition
If you don’t want take on the responsibility of secure asset disposition yourself – and many businesses don’t – working with a partner with expertise in ITAD is a smart option.
You don’t want to choose just any third party, though. Do your research and make sure they:
- Focus on compliance, not destruction or resale
- Have experience with embedded data and the IoT
- Will provide audit-ready chain of custody documentation
If a price seems too good to be true, it probably is. Some companies tend to cut corners and may not conduct a thorough data wipe before selling your assets. We saw how that worked out for the National Health Service in England.
As the NHS experienced firsthand, liability always traces back to the organization that created the data. Even after your IT assets are out of your hands, you are still the liable party, even if your third party does a shoddy job.
You also want to keep track of the exact hardware you give your ITAD partner. Make a list of serial numbers for yourself, but don't give it to your vendor. Ask them to confirm the products they have so that you know nothing got lost along the way. It’s also worth noting that the fewer parties involved in the process, the better.
Make IT Asset Disposition a Greater Priority
Hopefully this article helped you understand the role that asset disposition plays in your overall IT lifecycle and security. While it may seem like an afterthought, you can ensure that your assets are disposed of safely, protecting you from legal liability.
Think you know all you need about secure IT asset disposition to keep your company safe? Take our quiz to find out: